Amazing Tips About How To Become A Keylogger
To embody all features, we need to create a form and hide it from the user.
How to become a keylogger. Nowadays, there’ a variety of ways to. Overriding the basic setvisiblecore method will be enough. A password manager is a convenient way to avoid forgetting passwords and they’re also a great way to prevent keylogging attacks.
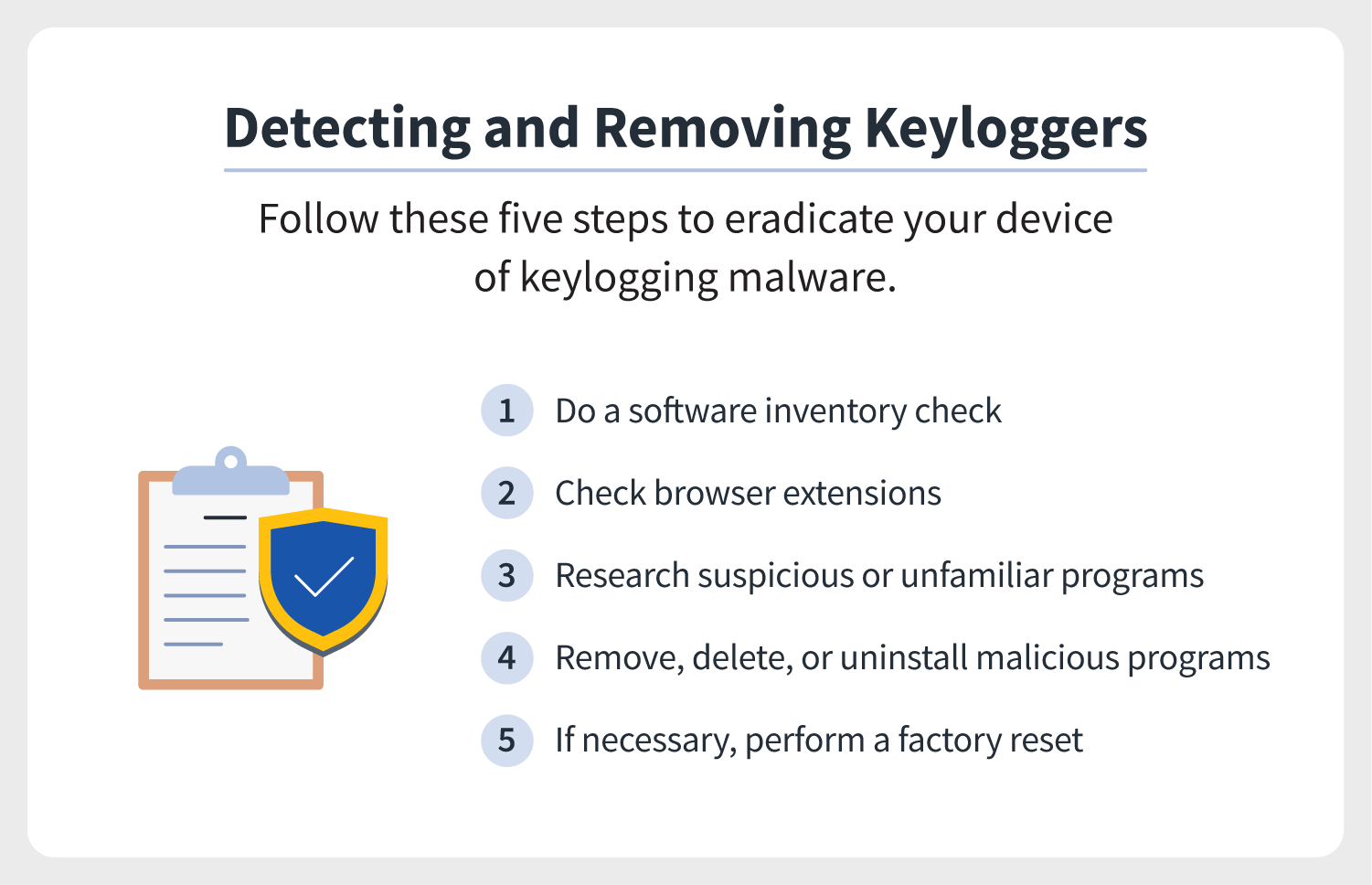
Implementing a python keylogger in just 10 lines from pynput.keyboard import key, listener import logging logging.basicconfig(filename=(keylog.txt), level=logging.debug, format=. How to install a keylogger by spear. Scan the device for malicious files:
How to install a keylogger: Examine the tasks running, and if you’re unacquainted any of them, look them abreast of an inquiry engine. A software keylogger is put on a computer when the user downloads an infected application.
Keyloggers tracks and records every key you press on the keyboard. The following are the four common methods that hackers use to install a keylogger on computers: The form will run at program startup.
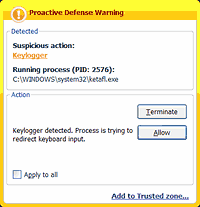
Press ctrl+alt+delete to check the task list on your computer. Go to the “ settings ” menu. Once installed, the keylogger monitors the keystrokes on the operating system you are using,.
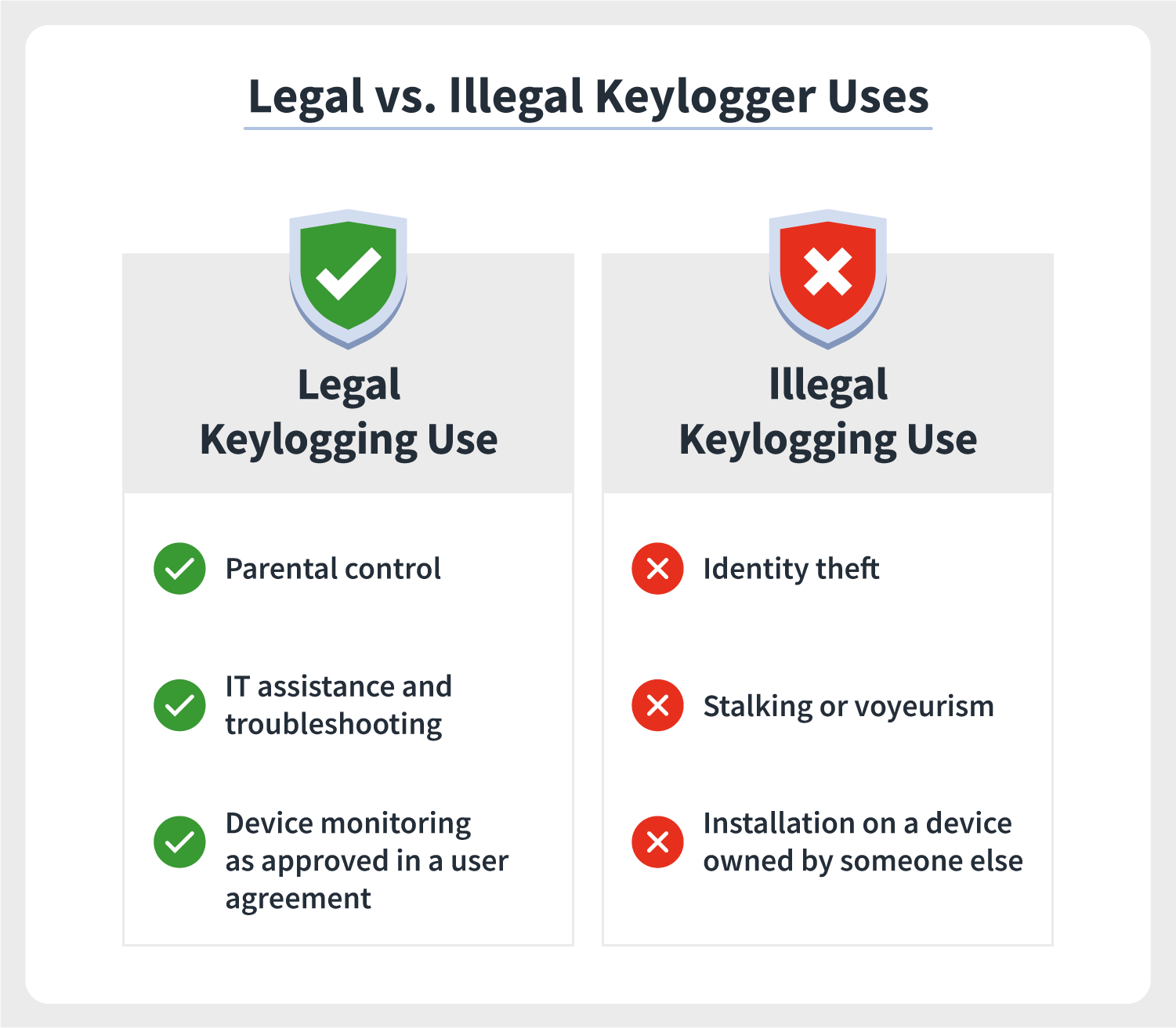
Keystroke monitoring of a public device. A spear phishing or fake email is one of the primary vehicles for keyloggers. Hackers will often attach malware containing keyloggers to emails and then disperse these emails to random.
A keylogger (also known as a keystroke logger and keylogging software) is a tool that records all keystrokes used by the monitored user. If you copy and paste your username and password, keyloggers won’t. Keyloggers are a particularly insidious type of spyware that can record and steal consecutive keystrokes (and much more) that the user enters on a device.
The temp folder quickly gets piled with clutter, making. Here’s how to install a keylogger on a router: Checking your internet usage report also is an effective way of confirming a keylogger’s presence on your system.
Malwarebytes for android can scan your device for. Up to 24% cash back since keyloggers are so harmful and detecting & removing them is a huge project, you had better take some measures to prevent you from. Copy and paste your username and passwords.
A software developer can make the keylogger using different. This app is used to spy on a spouse’s cell. Temporary files, or “temp” files, are a common place for keyloggers to hide.